The era of rapid AI generation has created a massive wave of insecure code flooding professional production environments. Most developers blindly copy snippets from large language models without checking for logic bombs or memory leaks.
This reckless behavior introduces critical vulnerabilities that traditional static analysis tools often fail to detect in modern stacks. You are likely sitting on a mountain of security debt that could collapse your entire architectural foundation today.
The Power of Professional Security Auditing
Implementing a rigorous AI code auditing framework feels like gaining a superpower that others simply do not possess. There is a profound sense of relief when you identify a buffer overflow before it hits the server.
You will feel total control over your hardware as your audited scripts run flawlessly on high end compute units. This mastery transforms you from a simple script kiddie into a true senior systems architect and lead.
Deploying Local Auditing Infrastructure
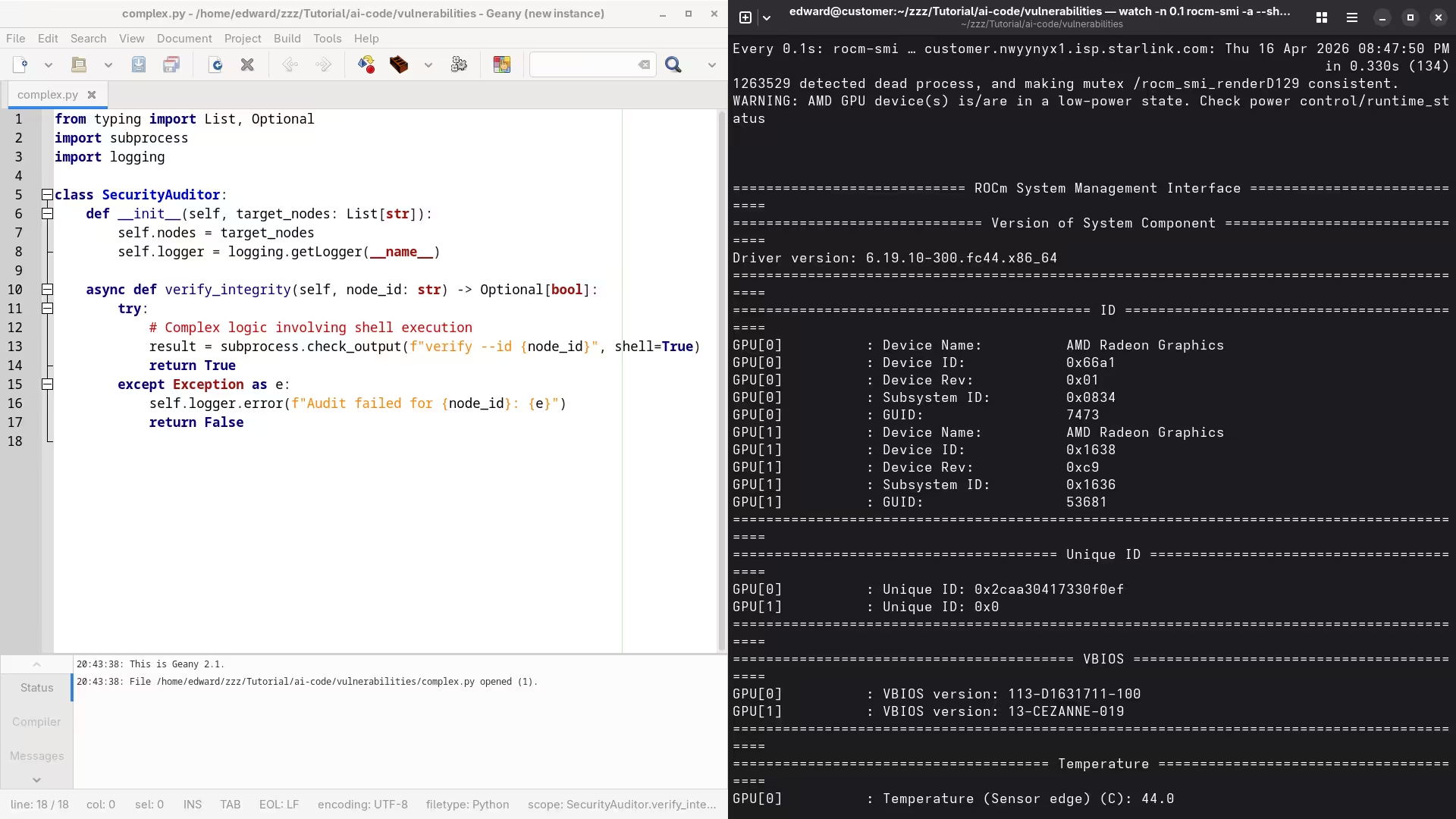
To begin securing your workflow you must deploy a local scanning environment that leverages raw compute power efficiently. We utilize the AMD ROCm stack on Fedora 44 to ensure that our auditing models remain entirely private.
Running these audits locally prevents sensitive proprietary logic from ever leaking back to third party cloud providers or competitors. This setup requires the specific installation of the hip runtime amd package to bridge the gap between Python and hardware.
Insider Configuration Secrets
One insider secret involves the specific configuration of the KFD kernel driver to allow large memory allocations for auditing. You must set the fragment size to at least two megabytes to handle massive codebase injections without crashing.
This adjustment prevents the dreaded out of memory errors when processing deep neural networks for vulnerability detection. Most enthusiasts miss this step and wonder why their local audits fail during heavy multi threaded operations.
| Parameter | Description | Value |
|---|---|---|
| Logic Flaw Detection | Standard Static Analysis | Poor |
| Logic Flaw Detection | AI Augmented Audit | Excellent |
| Logic Flaw Detection | Manual Architect Review | Superior |
| Parameter | Description | Value |
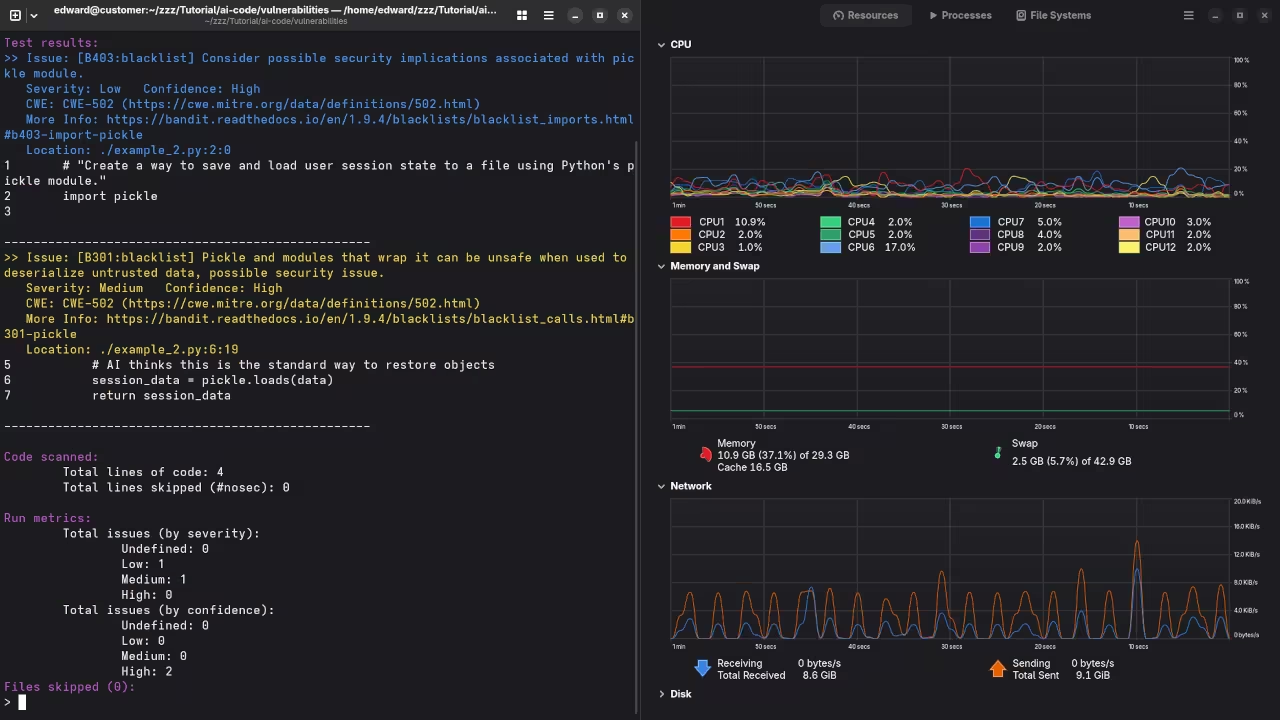
Automated Security Scanning Implementation
We can now look at a professional Python snippet designed to scan for insecure library imports automatically. This script targets common injection points and flags them for immediate manual review by the lead technical architect.
import os
import ast
def audit_code_security(file_path):
with open(file_path, "r") as source:
tree = ast.parse(source.read())
for node in ast.walk(tree):
if isinstance(node, ast.Import):
for alias in node.names:
if alias.name in ['pickle', 'subprocess', 'os.system']:
print(f"SECURITY ALERT: Risky import {alias.name} detected.")
audit_code_security("generated_script.py")
Integrating these custom security audits directly into your deployment pipeline ensures that every line of code is verified. This process mirrors our previous breakthroughs in Blender automation where we prioritized hardware stability and efficient resource management.
You can scale these auditing scripts to handle thousands of files by utilizing the parallel processing capabilities of the MI60. Mastering these local security audits ensures your infrastructure remains impenetrable while maximizing the potential of your hardware blueprints.
Master the Professional Stack
These advanced optimizations bridge the gap between basic coding and high level systems architecture found in my published guides. Secure your future by mastering the internal logic of the machines you build.
- Books (Technical Deep Dives): https://www.amazon.com/stores/Edward-Ojambo/author/B0D94QM76N
- Blueprints (DIY Woodworking Projects): https://ojamboshop.com
- Tutorials (Continuous Learning): https://ojambo.com/contact
- Consultations (Custom Architecture): https://ojamboservices.com/contact
🚀 Recommended Resources
Disclosure: Some of the links above are referral links. I may earn a commission if you make a purchase at no extra cost to you.
