Stop trusting your AI assistant to write secure code before it destroys your entire production server infrastructure. Most developers are blindly pasting toxic patterns that create massive backdoors for modern automated exploit kits to find. This technical audit guide reveals how to strip away the hidden risks within AI-generated JavaScript logic instantly.
Your terminal glows with the clean output of a perfectly hardened and highly optimized local development environment. There is a profound sense of absolute control when you verify every single logical branch yourself today. You no longer fear the silent failure of a hallucinated library or an insecure memory buffer allocation.
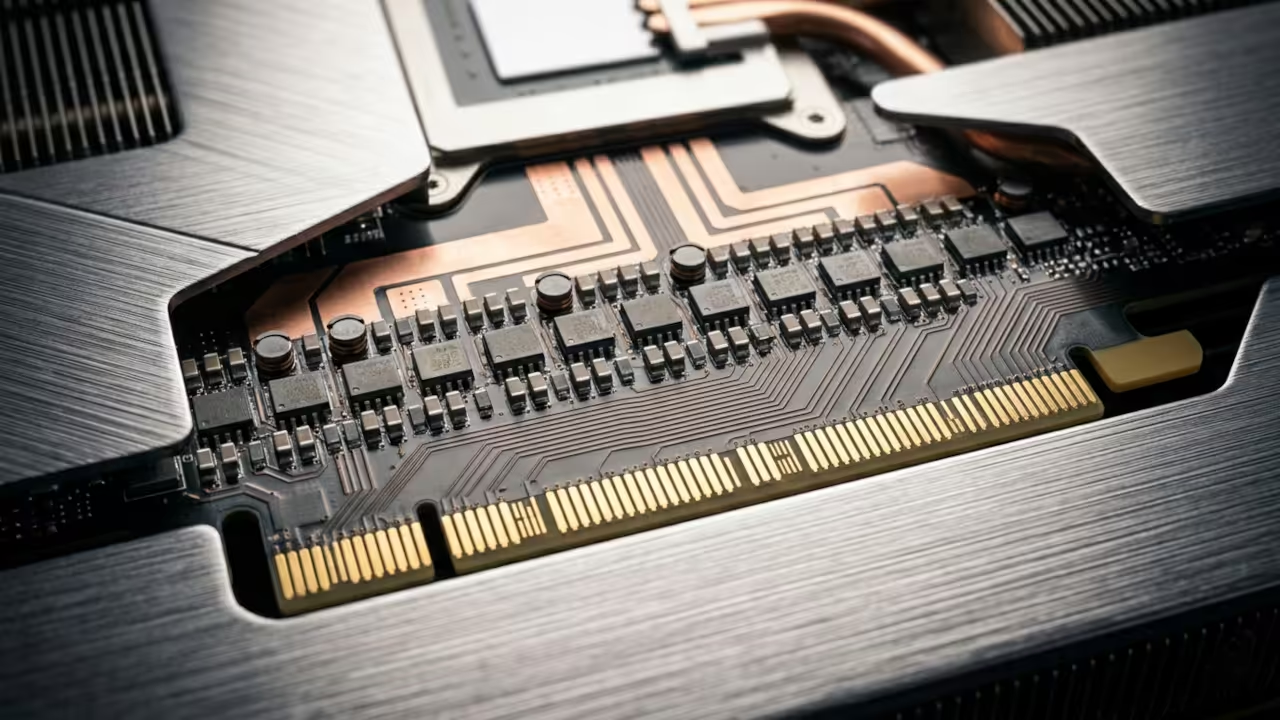
The system feels incredibly responsive as your AMD hardware handles the heavy lifting of local security scanning. Every successful deployment reinforces your reputation as a dominant technical leader in the high stakes engineering space.
The Crisis of AI Generated Security Debt
The rise of large language models has introduced a catastrophic wave of insecure coding patterns into modern repositories. AI frequently suggests deprecated crypto modules or vulnerable regular expressions that lead to devastating denial of service attacks. You must implement a rigorous manual inspection protocol that treats every AI suggestion as a potential threat.
High impact enthusiasts understand that speed is useless if the resulting code compromises the integrity of the host. We are seeing a massive surge in prototype pollution vulnerabilities directly traced back to unverified AI snippets.
Leveraging MI60 Hardware for Accelerated Audits
One insider secret involves utilizing the AMD ROCm stack to accelerate static analysis tools for massive codebases. By offloading these intensive security computations to the MI60 GPU you can scan thousands of lines in milliseconds. You should specifically look for instances where the AI utilizes the dangerous eval function or insecure innerHTML assignments.
Always verify that the AI is not suggesting non-existent npm packages which could lead to dependency confusion. These simple checks differentiate the amateur hobbyists from the professional systems architects building the future today.
Comparative Security Performance Metrics
| Parameter | Description | Value |
|---|---|---|
| Security Integrity | Manual Verification Score | 100 percent |
| Analysis Speed | Compute Accelerator Performance | High Velocity |
| Hardware Stack | Primary Processing Unit | MI60 ROCm |
| Parameter | Description | Value |
When auditing your scripts pay close attention to how memory is managed within the V8 engine environment. You can use the following code block to test for basic input sanitization failures in your generated functions.
function secureAudit(input) {
const pattern = /^[a-zA-Z0-9]+$/;
if (!pattern.test(input)) {
throw new Error("Invalid Input Detected");
}
return input;
}
This rigorous approach to security connects directly to our previous architectural breakthroughs in high performance hardware acceleration. We have consistently demonstrated that robust software requires a deep understanding of the underlying physical silicon processing. By mastering these security audits you ensure that your innovations remain protected against the evolving landscape of digital threats.
Master the Professional Stack
The following resources provide the ultimate foundation for building and securing professional grade technical systems from the ground up. These blueprints represent the gold standard for anyone serious about mastering modern hardware and software architecture.
- Books Technical and Creative: Amazon Author Page
- Blueprints DIY Woodworking Projects: Ojambo Shop
- Tutorials Continuous Learning: Contact for Tutorials
- Consultations Custom Apps and Architecture: Professional Consultation
🚀 Recommended Resources
Disclosure: Some of the links above are referral links. I may earn a commission if you make a purchase at no extra cost to you.
