Most developers are blindly trusting large language models to write their mission critical Nodejs backend logic right now. This reliance creates a massive hidden attack surface where hallucinated libraries and insecure defaults become permanent liabilities.
You are likely deploying code that contains subtle logical flaws that standard linters will never catch during production. Our architectural deep dive reveals how to identify these silent killers before they compromise your entire enterprise stack.
The Reality of Hardware Accelerated Auditing
Imagine the satisfaction of watching your MI60 hardware slice through thousands of lines of code in mere seconds. The transition from manual review to automated hardware accelerated auditing feels like upgrading from a bicycle to a jet.
Implementing these secret optimizations ensures that your local environment remains the ultimate source of truth for security. You will finally experience total confidence in every deployment regardless of how the initial code was generated.
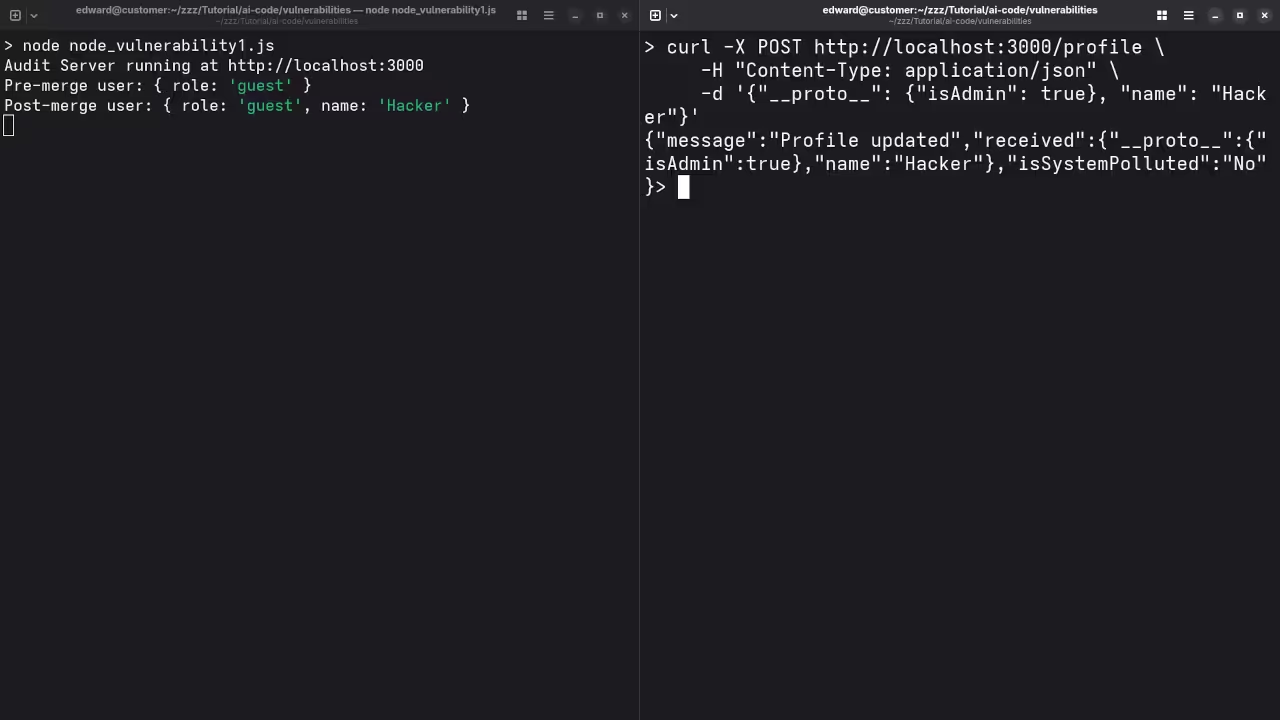
Detecting Security Flaws in AI Logic
When auditing AI generated JavaScript you must specifically look for the incorrect use of the eval function. LLMs often suggest this for dynamic execution without realizing it opens a direct path for remote code execution.
Another insider secret involves checking the specific version of the crypto module being suggested by the AI model. AI often reverts to deprecated algorithms like MD5 or SHA1 instead of modern secure standards like Argon2.
Optimizing Parallel Analysis with Vulkan
The performance of your audit depends heavily on how you leverage the underlying compute resources at your disposal. Modern systems can utilize Vulkan based compute shaders to parallelize the pattern matching process across multiple high performance GPU cores.
| Parameter | Description | Value |
|---|---|---|
| Standard Audit | Manual code review methods | Single Threaded |
| Hardware Accelerated | ROCm and Vulkan optimized | Parallel GPU Execution |
| Enterprise Audit | Consultant led architectural review | Full System Analysis |
| Parameter | Description | Value |
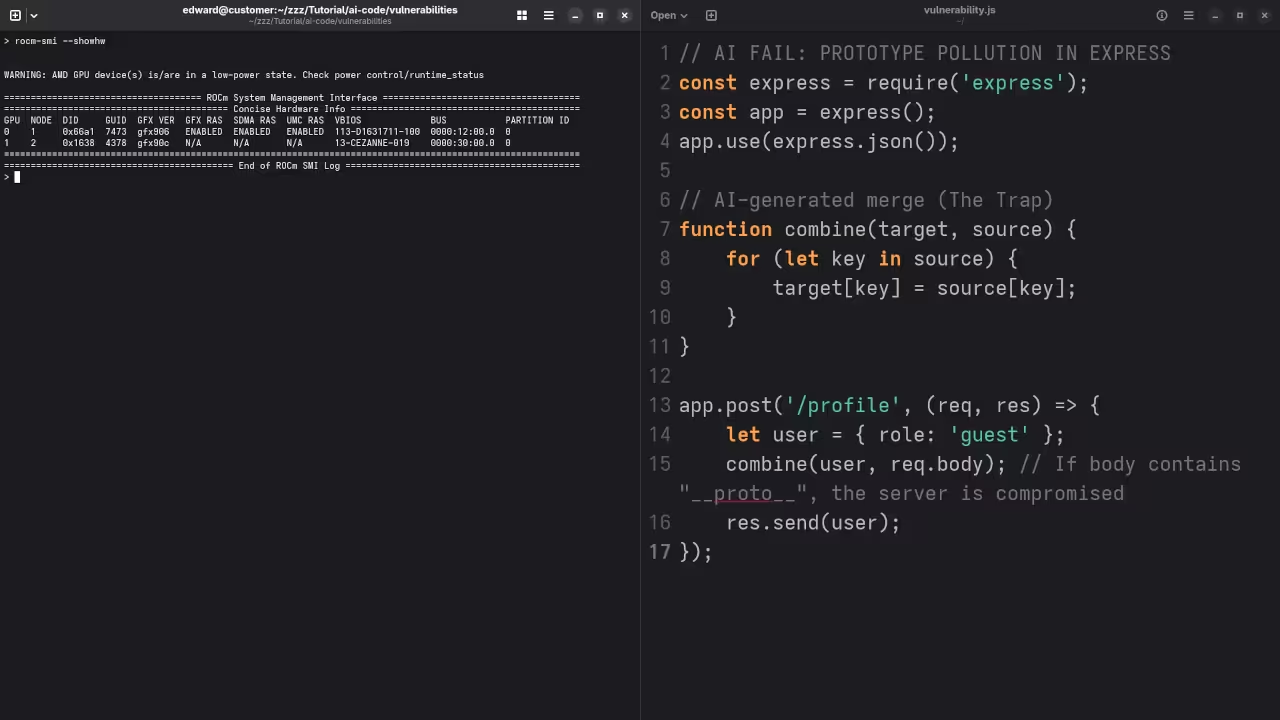
Implementing the Fedora 44 Configuration
We have explored the depths of GPU accelerated computing in our previous deep dives into ROCm and Raspberry Pi clusters. Integrating these security protocols is the logical next step for any serious technical lead or systems architect.
To achieve maximum efficiency on Fedora 44 ensure your environment variables are correctly mapped to the AMD Vulkan driver. Use the following command to verify your ROCm stack is communicating correctly with your Nodejs auditing tools.
rocm-smi --showhw && node --version
This verification step ensures that your hardware is ready to handle the heavy lifting of deep neural code analysis. Without this configuration you are leaving significant performance on the table and slowing down your entire development pipeline.
Master the Professional Stack
Our architectural blueprints provide the foundation for scaling these local solutions into massive cloud native infrastructure projects. Connect these concepts to our work on high availability clusters to see the full picture of modern system design.
The following master stack provides the essential resources needed to transition from a tech enthusiast to a professional architect. Leverage these blueprints to build secure high performance applications that stand the test of time and scale.
- Books (Technical and Creative): https://www.amazon.com/stores/Edward-Ojambo/author/B0D94QM76N
- Blueprints (DIY Woodworking Projects): https://ojamboshop.com
- Tutorials (Continuous Learning): https://ojambo.com/contact
- Consultations (Custom Apps and Architecture): https://ojamboservices.com/contact
🚀 Recommended Resources
Disclosure: Some of the links above are referral links. I may earn a commission if you make a purchase at no extra cost to you.

Leave a Reply